Working from home has its challenges for sure and one of those is your home network setup. And let me explain why. When you were working from your office, the network team was taking care of the network and probably also the security part of it, now that you are at home, it’s your responsibility. No matter if you work from home or not, your network is your responsibility. Just like you secure your house by locking, fence, cameras, etc, you also need to secure your network.
Probably when you work you use a VPN and you might feel secure but you are not. Many services are living in the cloud these days and those are not using a VPN. And even if you use a VPN that does not mean your network is secure.
There are many attacks against different home router vendors. And after a router is compromised, one of the first things that are changed is the DNS server. This way an attacker can direct home users to the servers that he wants and steal their credentials for example.
I gave this example because 2 of the elements from above, we can change/control to increase our home network security.
These are : your home router and the DNS server.
home router
Most ISP’s give a router when they install your internet. The problem with this is that in most cases this router is rarely updated to the latest version and even in the case that the vendor releases new software this needs to go through your ISP. This usually takes a lot of time or never get’s pushed. Because of this, your home router could be compromised. Also after it is compromised your router might become part of a botnet.
In some other cases, your home router has some services opened to the internet so that the ISP can do remote administration. These can also be used by an attacker in some cases.
In other cases, the admin password for these devices is not secure enough and can be brute-forced.
The bottom line is that your home router is not secure enough.
What you can do is to not trust your ISP router and buy a router that you can manage/control and that can be updated more frequently. And even after that, you need to follow some basic rules like: change your admin password to a stronger one, do not open services to the internet and set up a basic firewall, change the wifi password, keep the OS up to date, etc…
DNS server
The home router provided by an ISP usually has the DNS server settings pointing to the ISP servers. These days this is not advisable. So what you can do is use a more secure option, like Cloudflare DNS, Google Public DNS, OpenDNS, Quad9 DNS. (find more info here:https://www.techradar.com/news/best-dns-server).
Cloudflare is pretty fast and it is very privacy-oriented. It also has a service for families that provides “protection to your home network and protect it from malware and adult content”.
1.1.1.2 (No Malware) & 1.1.1.3 (No Malware or Adult Content)
“Quad9 blocks lookups of malicious hostnames from an up-to-the-minute list of threats. This blocking action protects your computer, mobile device, or IoT systems against a wide range of threats such as malware, phishing, spyware, and botnets, and it can improve performance in addition to guaranteeing privacy.”
DNS servers: 9.9.9.9 and 149.112.112.112
OpenDNS “The free service offers plenty of benefits: high speeds, 100% uptime, phishing sites blocked by default, optional parental controls-type web filtering to block websites by content type”
If you want to go a step further you can set up your own DNS at home using a Raspberry PI and Pi-hole for example.
My setup
In my case, I’ve used a Mikrotik router, Pi-hole as a local DNS server that is pointing using DoH to OpenDNS server.
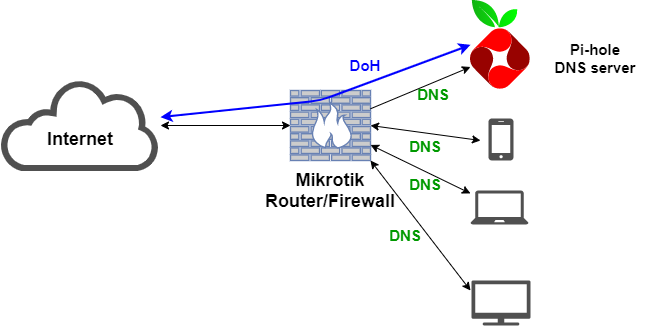
I’ve used a Mikrotik router because the vendor provides updates a few times a year and it is under my control, not the ISP. It has a Linux-like firewall with plenty of features. You can even have scripts on it and automate some tasks. I am using such a task to download some backlists and update a firewall rule that is blocking those.
The DCHP of the firewall is pointing to an internal DNS. This internal DNS server is using Pi-hole. “The Pi-hole is a DNS sinkhole that protects your devices from unwanted content, without installing any client-side software.”
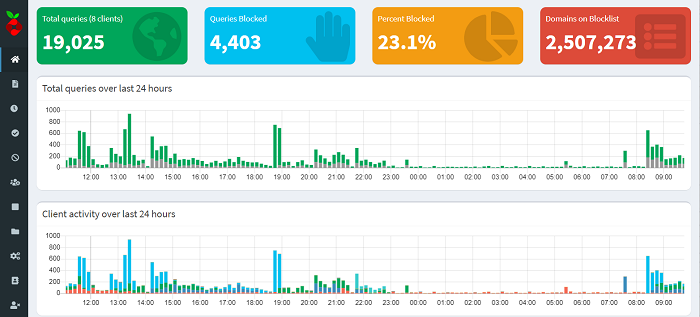
This server is configured to fetch DNS info from OpenDNS using DoH(DNS over HTTPS). This way my DNS request can not be seen by the ISP for example. It can also be configured to download blacklists and to block known bad/advertising hostnames. The other good thing about Pi-hole is that it gives you visibility on what your home devices are requesting. This way I saw that most of the DNS traffic was done by my smart TV. You can also start blocking whatever hostnames you want as it has a blacklist, whitelist feature.
OpenDNS provides an optional parental controls-type web filtering to block websites by content type. It can also provide Malware/Botnets protection, Phishing protection.
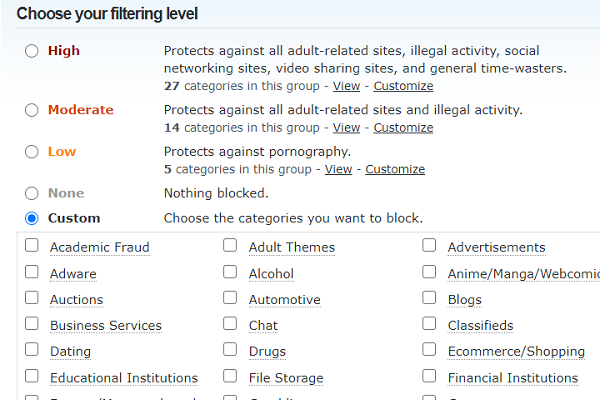
In my case at the DNS level, some things get blocked by Pi-hole and some by OpenDNS.
If you are not a tech savvy person, and managing/configuring a router/firewall and a DNS server is too much for you, the most basic thing that you can do is to use a safe fast DNS server like the ones I have mentioned above.